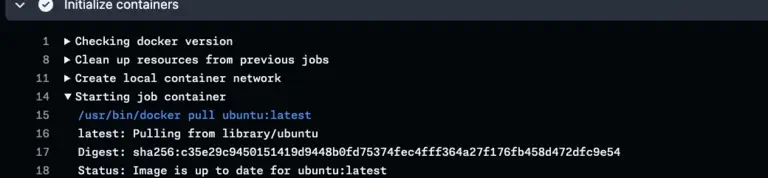
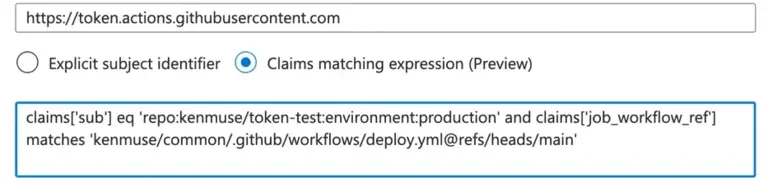
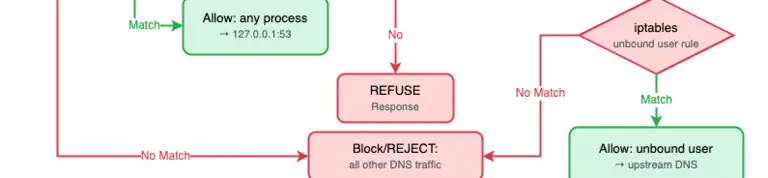
Sometimes you need to configure the workflow’s runner dynamically before it runs any steps. For example, you may need the runner to get access to a set of secure resources. This post shows how to use OpenID Connect (OIDC) tokens to avoid storing secrets or using long-lived credentials.

Ken Muse