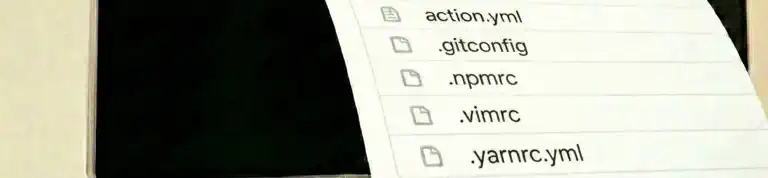
Your dotfiles repository already personalizes your development environments, but what if it could do more? What if the same configurations that protect your local machine could secure your CI/CD pipelines? By adding a simple composite action to your dotfiles repo, you can apply security settings and configurations to any GitHub runner – without managing tokens or cloning anything yourself. Let me show you how.

Ken Muse